Table of Contents
Abstract
The analysis detailed in this paper acts as a network infrastructure for Worldwide Advertising, Inc. (WAI). The network is comprised of different areas, which are detailed in the document. It is important to recognize the fact that each segment of the network plays a very important role in the operation of the system. They all work together to ensure that Worldwide Advertising, Inc. (WAI) has a secure and efficient communication network between New York and Los Angeles. In this paper, a detailed explanation of the process of deploying Windows Server 2012 will be provided together with the requirements for ensuring that there is a secure network for use by Worldwide Advertising, Inc. (WAI) in the future.
Introduction
Worldwide Advertising, Inc. (WAI) is a firm that specializes with advertisements. The firm has offices situated in New York and Los Angeles. They are currently scouting for a network solution that is both secure and reliable for the operations. The solution that will be adopted by the firm should be able to accommodate the company’s staffs who are about 300 in number and also be able to meet the needs of the company within the next three years. Worldwide Advertising, Inc. (WAI) currently lacks an internal IT department but they plan to have one set up in the future. Once the company has been able to hire the right personnel to run the department, they will take over from the person currently operating it. As an IT professional, I have been tasked to supply Worldwide Advertising, Inc. (WAI) with a solution that will be appropriate for its core services. The cost of implementing the proposed solution must be able to meet the needs of the company and within the company’s budget.
Deployment and server editions
As an IT expert, my task is to provide solutions to the company structure of the network and the server. Some of the crucial information that will be included in the network and server structure includes the strategy for the deployment of the servers and the editions that are best fit for the company needs (Ciampa, 2012). Details on the number of servers that will be required and the most appropriate location for each one of them will also be given. To deploy the network, four servers will be required. Since most of the employees are based in Los Angeles, three of the server will be located there. The remaining one server will be located in the New York office as it has a smaller number of employees. At each location, Windows Server 2012 Data center edition will be used in the servers. This version will be quite appropriate for the company as it will also at least 4 terabytes of memory; it supports 64-bit processor chips and will also allow a large number of virtual devices to be connected to the network (Stanek, 2013).
It will be important to ensure that each of the four servers is virtualized. The 2012 version of the Data Center edition comes with HPV capabilities. Virtualization of the servers will enable multiple servers to be created on the deployed physical servers (Ciampa, 2012). Virtualization helps organizations to cut down on the cost of maintaining the high number of physical servers that may be installed to make the system operational. Virtual servers also enable the system administrator to allocate spaces on the servers based on the organizational needs (Ciampa, 2012). To deploy the servers, the most appropriate method will be through the use of a Windows-Installer based version. In selecting the method of deployment, it will be crucial to consider the size of the organization. Worldwide Advertising, Inc. (WAI) is a mid-sized firm and has hundreds of users. Therefore, Microsoft Application Virtualization (App-V) which is a form of virtualization technology will be applied. This approach will help cut down on the cost as well as enable reaching of a larger number of employees within the company.
DNS
A domain name will be used to identify the IP address of the organization. Since Worldwide Advertising, Inc. (WAI) aims to have its presence on the web to make it more accessible, it will be important for them to have a web address which will be identified by a URL. Taking into consideration the nature of their business, Worldwide Advertising, Inc. (WAI) should have a domain that ends with a top level domain (TLD) such as com which is given to commercial organizations. The company’s domain will be www. Worldwide_advertising.com. As Stanek (2013) indicates, the main use of the domain is to enable the DNS to translate to the IP address.

A secondary DNS server will have to be added to a second site. The server will help to provide fault tolerance and load balancing when the servers are in operation. Secondary DNS servers also help to maintain zone data in read only format. The DNS clients can also be configured to query the secondary DNS rather than the primary DNS for a particular zone (Stanek, 2013). This is only implemented by reducing the demand for the primary servers thereby making them available for deployment at all times. To add the secondary DNS server, the prospective DNS server will be added to the list of the name servers. The transfer settings will then be verified on the DNS server and the secondary DNS server added as a secondary zone in the network. Having a second site on the domain helps to secure the network and improve performance.
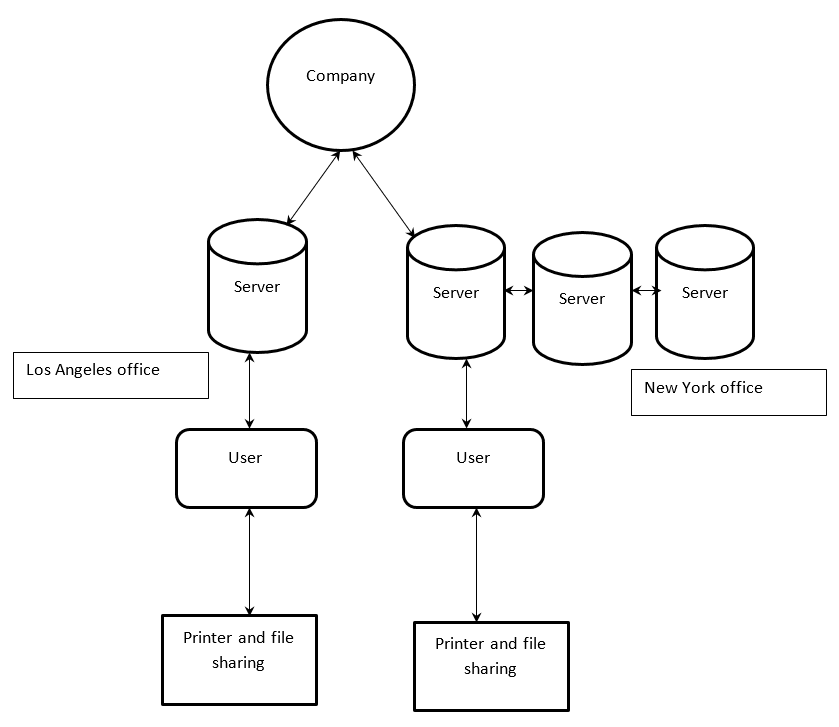
Figure 1: AD design and DNS namespace
Active Directory
The network will be comprised of a number of Active Directory domains, whereby each one of them will have a unique name. Windows Server 2012 will use Microsoft Active Directory Domain Services to build a distributed network. The Active Directory domains will help to locate and work with different objects including printers, data storage devices, printers, among others (Russinovich, & Solomon, 2009). There will be two different d Active Directory domains each for the two locations. At New York, the Active Directory domain will be called WAINY while that at Los Angeles will be called WAILA. Since the servers are located in two different cities, the domains will be considered as points of replication.
Within the network, there will be read only domain controllers. The domain controllers will contain data on domain partition which is usually replicated when the controller is within the same domain (Stanek, 2013). The domain partition store will hold data about objects that are located within the domain. To secure the data, the domain controllers will be read only, which will ensure that data contained in the servers cannot be altered or deleted by an unauthorized personnel (Russinovich, & Solomon, 2009). The second site will be configured into the domain controller placement by placing additional domain controllers. This will be implemented during the process of partitioning whereby additional domain controllers will be placed to take care of the second site. The number of additional domain controllers that will be created will be determined by the distribution of the load and the tolerance of the network to faults.
The configuration of the AD sites will be configured using a very simple approach. First, at least two different domain controllers will be created. This will help to ensure that all the looming points of failure are fully eliminated. For both the first site and the second site, the wide area network (WAN) will be selected to handle the failover. Finally, to handle the client workload, the additional domain controllers will be placed into the site and deployed to handle the site operations.
File and printer sharing
For one to enable the file and printer sharing options in Windows Server 2012, he would be required to have the group policy management tools on windows 12 servers (Stanek, 2013). This will require the use of Remote Server Administration Tools (RSAT) tools which are available on Windows Server 2012. The system administrator will be required to open the file sharing ports in order to enable sharing options. The inbound rules to the windows firewall will have to be changed to accommodate sharing (Russinovich, & Solomon, 2009). Using the Windows 2012 Virtual Server, the administrator will be able to connect to change the firewall details to receive inbound results. Having done this, users can be able to access files and print documents from any connected device within the network.
To configure the quotas in the network, there will be need to use the File Server Resource Manager (FSRM) Microsoft Management Console (MMC) snap-in. Using FSRM, it will be possible to create limit the space using quotas and notifications will be generated when the limit is reached or exceeded (Russinovich, & Solomon, 2009). For this company, 500 MB limits will be placed for personal folders, 1 GB limit will be placed for group folders and 2 GB limit will be applied for the temporary folders. The actions pane which is found on the FSRM will be used to alter and change the thresholds, quota and the requirements whenever there is need to do so (Stanek, 2013).
A Distributed File System (DFS) namespace will also be implemented. The DFS will enable the system administrator to share files that are located in various servers by ensuring that they are connected to one or more DFS namespaces. The DFS will give a virtual overview of the shared folders within the firm. The system administrator will also be able to provide the namespaces for the hierarchy within which the folders are available in. Network users will also be able to navigate through the different folders with having to know the names of the servers or the data on which they are hosted. According to Russinovich, & Solomon (2009) the Distributed File System (DFS) capabilities improved the loading capabilities of the network and also improve the network tolerance to faults.
We can do it today.
Conclusion
From the analysis carried out above, the nature of the network has been fully provided. The process that will be used in the deployment and administration of the Windows Server 2012 has been described in detail. Worldwide Advertising, Inc. (WAI) will be required to ensure that they invest in a highly competent IT team who will take over from the network implementation team after the network has been set up. It is recommended that the team should be trained on the operations of the network and work under supervision for some time before they can fully take over.
- Ciampa, M. (2012). Security+ guide to network security fundamentals. Cengage Learning.
- Russinovich, M., & Solomon, D. A. (2009). Windows internals: including Windows server 2008 and Windows Vista. Microsoft press.
- Stanek, W. (2013). Windows Server 2012 inside out. Pearson Education.
